On April 10, 2025, the digital systems of OTP Bank were hit by an unprecedented overload cyberattack. As a result of the so-called Distributed Denial of Service (DDoS) attack, which lasted for several hours, the bank’s customers were periodically unable to access their internet banking, mobile banking application, and other digital platforms. The slowdown and complete shutdown of services not only hindered customers’ daily banking but also generated significant nationwide attention.
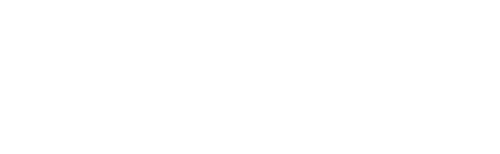
DDoS attack map – visual data traffic
According to a report by Portfolio, OTP’s digital infrastructure was hit by an “unusually large-scale overload attack,” during which a massive flood of data requests from external sources inundated the servers, making the systems virtually inaccessible to genuine users. Based on expert feedback, the attack was not only unusually strong but also of historical proportions: according to some estimates, the volume of requests hitting OTP’s systems at times may have equaled the entire internet traffic of Hungary. This level of load could represent the simultaneous activity of several million devices operating from various parts of a world, all under the control of a central botnet network.
In modern overload attacks, even robotic vacuum cleaners, smart refrigerators, or TVs can act as “soldiers,” participating in the attack without the users’ knowledge. At first glance, these devices seem harmless—for example, a smart toothbrush, a security camera, a smart speaker, or even an internet-connected children’s toy—but if their software is vulnerable or improperly configured, an attacker can take control of millions of them at once. Since these are scattered worldwide in home networks, they cannot be simply blocked or shut down, meaning the attack traffic comes from an almost impossibly diverse range of sources. This gives rise to one of the greatest challenges of DDoS attacks: attackers can participate in global overload attacks even through our home Wi-Fi—without us knowing anything about it.
OTP reacted immediately and confirmed in an official statement that the attack did not result in data loss or unauthorized access. However, they emphasized that it was an “unusually large-scale overload attack even by international standards“, which significantly complicated customer service. According to an article by Index, the goal of the attack was not data theft or intrusion, but to paralyze OTP’s digital services by extremely increasing traffic. The bank’s systems were operational, but the external access points were overloaded, preventing customers from connecting and executing transactions.
Although the target this time was one of Hungary’s largest banks, the phenomenon extends far beyond the problem of a single institution. With the increasing prevalence of digital services, cybersecurity threats have also reached a new level. The incident against OTP is a warning sign for all organizations: a well-organized, technically advanced attack can cause not only financial damage but also customer loss, a decline in trust, and long-term reputational harm—even if data security itself is not compromised.
What is a DDoS attack, and why is it so dangerous?
A Distributed Denial of Service (DDoS) attack is one of the most well-known and frequently used types of cyberattacks. Its essence is that attackers intentionally flood a server, website, or digital service with a huge amount of—typically fake—data traffic, thereby making it impossible for normal users to access it. During a DDoS attack, the “tsunami of requests” does not come from a single machine; instead, many thousands, often tens or hundreds of thousands of devices, participate simultaneously. These devices—infected computers, servers, and smart devices organized into a so-called botnet—are often at the attackers’ disposal without their owners’ knowledge. With the help of such a global botnet, attackers can generate a massive volume of traffic and direct it at a specific web service.
It is important to understand that DDoS is not the same as hacking or data theft: its goal is not to breach the system, but to paralyze it. To illustrate this with an everyday example: imagine a restaurant with a single entrance where guests can enter and dine. A DDoS attack is like thousands of people suddenly appearing at the door—not to actually eat, but to pound on the door, ask questions, make reservations, and then disappear all at once. The staff cannot distinguish between real guests and the artificial noise, so no one can be served. The system does not technically collapse, but it becomes practically unusable—this is the essence of DDoS. This means that although the backend systems often remain intact, from the users’ perspective, the service is down—which can be catastrophic from both a business and reputational standpoint.

When ten thousand bots knock on the server’s door at once
The public is most familiar with high-volume, flooding attacks—where gigabits of data traffic block a service—but so-called “starvation” DDoS attacks are at least as dangerous. In these cases, the goal is not bandwidth saturation but targeted resource exhaustion. For example, if an attacker initiates thousands of intentionally unfinished TCP connections per second, they can tie up the servers’ memory and CPU, completely paralyzing responsiveness—even with as little as 6 Mbit/s of traffic, as demonstrated by several domestic cases in the past, besides the recent OTP incident.
Detecting such an attack depends not on the volume of traffic, but on identifying abnormal patterns. A good defense system not only measures traffic but also analyzes its structure: for example, how many connections remain incomplete, how many similar requests arrive from the same IP address, or how much the traffic profile deviates from the norm. To use an everyday analogy: it is as if ten customers enter an OTP bank branch, and each of them needs to register a new ID card. This in itself is not a problem, but if all ten customers request a lengthy data verification process at the same time, the bank teller will quickly become exhausted. And although the branch is not full, service comes to a complete halt—this is exactly how a starvation attack works: low visibility, but highly effective paralysis.
Therefore, DDoS is not just a technical problem, but a business risk. Anyone who operates digital services—be it a bank, a webshop, a healthcare system, or even a municipal portal—now has a strategic interest in being prepared to fend off or quickly mitigate such an attack.
How can we defend against DDoS attacks?
One of the greatest dangers of DDoS attacks is that they occur suddenly, without warning, and can paralyze an organization’s digital operations in moments. Therefore, the key to defense is not just a rapid response, but also proactive preparation, active monitoring, and a flexible infrastructure.
The first step is traffic monitoring: a modern IT system must be able to monitor data traffic in real time and detect abnormal patterns—such as a sudden increase in the number of requests or suspicious sources. Overload attacks could often be filtered out in the first few minutes if the infrastructure had the right sensors and alert systems.
The second step is traffic filtering and routing. An effective DDoS defense can automatically distinguish between real customer requests and attack traffic, allowing only the former to pass into the system. This is important not only at the network layers but also at the application layer: for example, if the attack targets specific web applications and not just IP addresses.
It is important to note that traditional firewalls alone are not suitable for mitigating DDoS attacks. The primary task of a classic firewall is to manage access rules: for example, who can access a specific port or protocol. While these systems are capable of some level of simple traffic filtering, they do not analyze the structure of the traffic and cannot distinguish in real time between legitimate users and attacking bots. Moreover, if a huge amount of data suddenly arrives, the firewall itself becomes a target, and it is not uncommon for it to be simply overloaded before the attack even reaches the internal systems. Modern DDoS protection is therefore multi-layered: it consists not only of a firewall but also of specialized traffic analyzers, dedicated filtering devices, and—in the case of larger-volume attacks—cloud-based diversion systems, which work together to recognize the type of attack and react automatically accordingly.
A scalable infrastructure is also essential. Most traditional servers cannot withstand a DDoS load—this is where cloud-based traffic management comes into play, which can distribute the load across multiple servers or data centers, preventing a shutdown.
The third, often overlooked but critically important step is setting up rule-based automatic response systems. These allow the system not only to signal an attack but also to react immediately—for example, by blocking IP addresses, redirecting traffic, or temporarily restricting the given service while the emergency persists.
However, the defense does not end when the attack is over. The post-attack analysis, evaluation of log files, and system responses can provide important lessons for preventing future incidents. This is particularly important in sectors with critical business operations—such as finance, healthcare, or e-commerce.
Unicorn can not only provide assistance in responding during attacks but can also proactively test the state of DDoS protection. Using a simulated overload traffic—without causing a live system outage—we can assess how well a given IT infrastructure would hold up in a real attack. We provide development recommendations for the weak points identified during testing, so the defense can be strengthened not only in theory but also in practice.

Real risk in simulation – this is how digital defense can be strengthened
This service is particularly important for organizations that bear operational or financial risk from a DDoS event—as they can obtain valuable information about the state of their own defense system without suffering real damage.
The defense measures above clearly show: protection against DDoS does not depend on a single tool, but on a complex, well-coordinated defense strategy. Developing this strategy requires experience, a technological background, and the right professional partner.
Reliable DDoS protection from Unicorn – By integrating market-leading technologies
To effectively fend off DDoS attacks, a quick reaction is not enough—a pre-built system is needed that can identify and neutralize the threat in the very first seconds. The DDoS protection solutions integrated by Unicorn exist for precisely this reason: they provide real-time, flexible, and customizable protection against the most diverse types of overload attacks.
The operation of the systems used by Unicorn is based on a multi-layered defense logic that can handle attacks targeting both the network (Layer 3 and 4) and the application layer (Layer 7). This is particularly important because modern DDoS actions not only generate simple IP traffic but also try to overload the infrastructure with complex, application-level requests—for example, with targeted website or API calls. These solutions perform real-time data collection and traffic analysis, so the system immediately recognizes unusual patterns. As soon as signs of an attack appear, pre-configured response measures are automatically activated: blocking IP addresses, restricting or redirecting traffic, or other flexible response mechanisms.
One of the most important advantages of the system is cloud-based DDoS protection, which is not just a technological solution but a strategic step forward compared to traditional, locally operating defense tools. While a more serious attack can quickly push local infrastructure—such as a physical hardware DDoS device—to its limits, a cloud-based system can handle the increased traffic with virtually unlimited capacity. For attacks of this volume, a locally installed hardware DDoS filter is no longer sufficient, even if it is a state-of-the-art device. The most advanced solutions currently in use include technologies such as those from Radware, Arbor, or NetScout—the latter of which Unicorn also applies as a recommended solution. These are capable of diverting all network data into a secure, high-capacity “digital space,” where legitimate requests are automatically separated from attack traffic. This can be imagined as traffic control opening a separate lane for ambulances in a crowd: the traffic of real customers proceeds on a protected, dedicated channel, while robotic or malicious requests are diverted and neutralized. Thus, the defense is not only effective but is activated practically instantly and automatically as soon as the system detects abnormal patterns.
In the solution offered by Unicorn, the locally installed defense infrastructure is in constant contact with the manufacturer’s highly advanced cloud-based system. As soon as the detected load reaches a preset level, the system automatically initiates the diversion of traffic to the cloud. There, the data is analyzed, filtered, and cleaned—meaning the attack traffic is separated, while real, legitimate customer requests are returned to the corporate infrastructure through a secure, dedicated channel. This architecture not only makes it possible to effectively neutralize even the largest-scale attacks but also to maintain service continuity without information loss. Moreover, cloud-based protection can be fine-tuned, meaning it can be configured according to the client’s needs to determine in which traffic situations it should activate and what automatic reactions should follow the detection of an attack.
Experience—including the recent attack against OTP—shows that overload actions of this magnitude can only be managed effectively with cloud-based assistance. The systems used by Unicorn are backed by the market’s most advanced DDoS protection technologies—including NetScout, which the company specifically recommends for fending off extreme loads, as the system they developed enables real-time response and extraordinary load management.
As we wrote earlier, however, protection does not end with repelling the attack. Unicorn’s experts also provide post-incident analysis, helping clients become more resilient to future threats by evaluating the characteristics of the attack. In addition, regular consulting and operational support ensure that the protection functions stably in the long term. Whether a company operates in the financial sector, e-commerce, or another critical digital service, Unicorn’s DDoS protection provides secure operation, continuous availability, and a rapid response even against the most sophisticated attacks.
The solutions applied by Unicorn enable real-time response, prevention, and the drawing of post-incident lessons
In addition, it is important to emphasize that protection against an overload attack is crucial not only from a technological but also from a regulatory perspective. In the financial sector, the Hungarian National Bank (MNB) has previously imposed fines for IT deficiencies, especially if they resulted in disruptions to customer service. The European Union’s DORA (Digital Operational Resilience Act) regulation, which will be mandatory from 2025, will require ensuring digital operational resilience, which may also include DDoS protection and its testability.
A financial institution, therefore, has not only a technical but also a legal responsibility to ensure that its infrastructure is prepared for overload attacks. This compliance is not only a regulatory expectation but can also be a market competitive advantage—while its absence can lead to fines, reputational risk, and even business losses.
Summary
DDoS attacks are no longer rare exceptions but are among the everyday threats of the digital world. Prevention, awareness, and professional protection are crucial not only for business continuity but also for maintaining customer trust. The unprecedented OTP incident has shown that anyone can become a target, but who can stay standing depends on preparation and good decisions. In this, Unicorn is not just a technological partner, but a strategic defense ally.